Awesome GitHub features you probably didn't know

Do you really think you know everything about Github? Let's find out!
Here you have 4 GitHub features I found while I was working in a new project.
1. Special repository
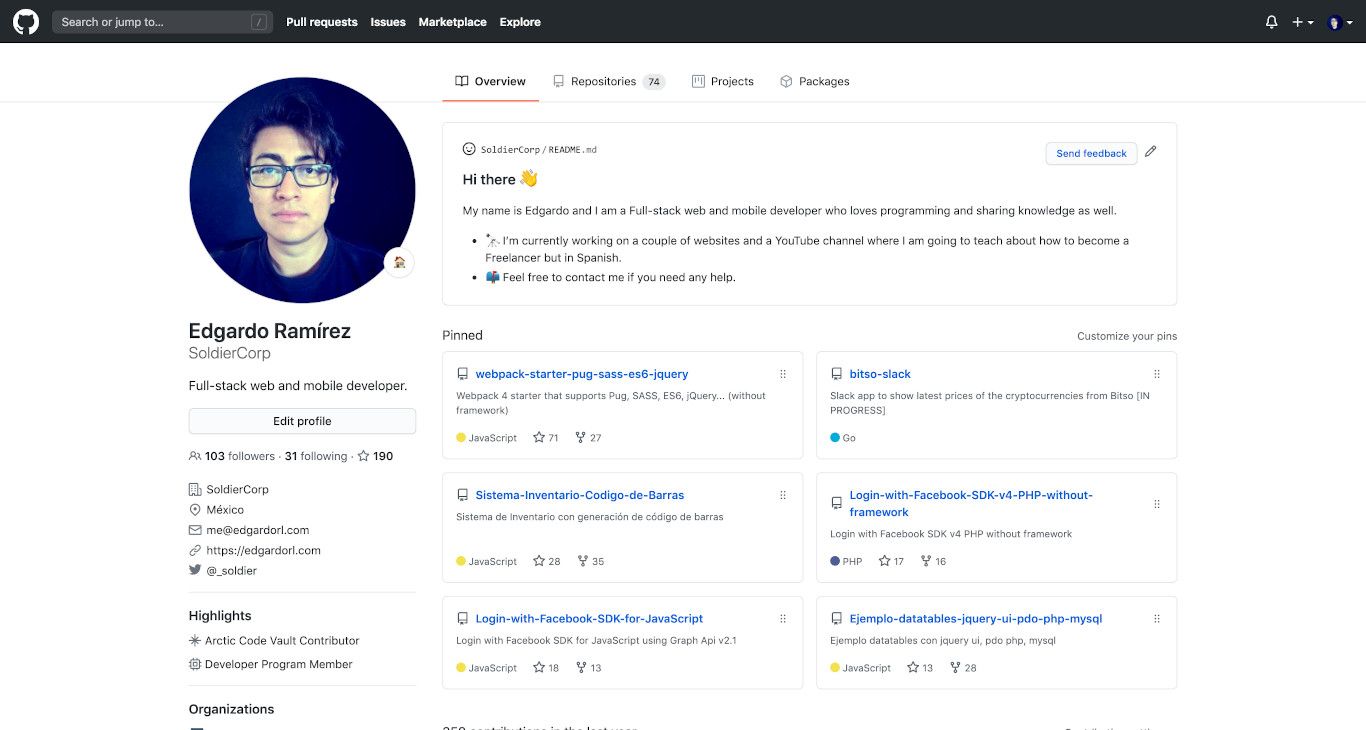
You can have an extra box in your GitHub profile (above image) to write more info about you if you create a repository and name it as your username.
For example, if your username is edgardo then create a public repository with a README.md and name it edgardo then you will see an alert box saying that you are activating a special repository.
The README.md file will come with default information to show you what you can do in that file. Go ahead and create yours!
2. CODEOWNERS file
People with admin or owner permissions can set up a CODEOWNERS file in a repository and is a file where you can define individuals or teams that are responsible for code in a repository.
The main goal of this is that every time you open a Pull Request all the owners listed in this file will be automatically requested for review without manually let them know as usual.
In order to have this feature enabled, you need to create a new file named CODEOWNERS in the root, docs/, or .github/ directory in the repository and in the desire branch.
This is the basic syntax you can use in this file where all these users will be notified for a review in every PR you submit.
* @edgardo @simon @george
More information about this file: https://docs.github.com/en/github/creating-cloning-and-archiving-repositories/about-code-owners
3. Codespaces
Is a new feature that (as they say) you can get the full Visual Studio Code experience without leaving GitHub.
This means you can code directly in your browser in the same way you do in your local machine but this time you don't need VSCode or any other code editor but only your browser like a instant development environment.
You will be able to code, build, test, debug, and deploy from Github Codespaces.
More information about Codespaces: https://github.com/features/codespaces/
4. Secret scanning to prevent fraudulent use of secrets
GitHub performs a secret scan in every repository to detect for known file types or secrets that could contain sensitive information about your project itself like an .env file or a password or a secret token.
This is really awesome because out there exists tools than can scan into the GitHub repositories looking for these files too but the goal is different since anyone can use them and get important information about your repository if you forgot to remove that sensitive information.
More information about secret scanning: https://docs.github.com/en/github/administering-a-repository/about-secret-scanning
